Cyber Risks in the Industrial Scheme
Eric Olson | September 07, 2017 Programmable logic controllers (PLC) that are part of an industrial control system (ICS) for a membrane bioreactor system at the Tenino Wastewater Treatment Plant in Washington state. Credit: Eric Shea / CC BY 2.0
Programmable logic controllers (PLC) that are part of an industrial control system (ICS) for a membrane bioreactor system at the Tenino Wastewater Treatment Plant in Washington state. Credit: Eric Shea / CC BY 2.0
Industrial cyberattacks are becoming increasingly widespread. In Kaspersky Lab’s 2017 report on the State of Industrial Cybersecurity, 55 percent of organizations surveyed experienced at least one cybersecurity incident in the past 12 months. Industrial control systems present prime targets for cybercriminals. They monitor and control industrial processes and come in a variety of configurations, including supervisory control and data acquisition (SCADA) systems, distributed control systems (DCS), process control networks (PCN) and other industrial automation systems.
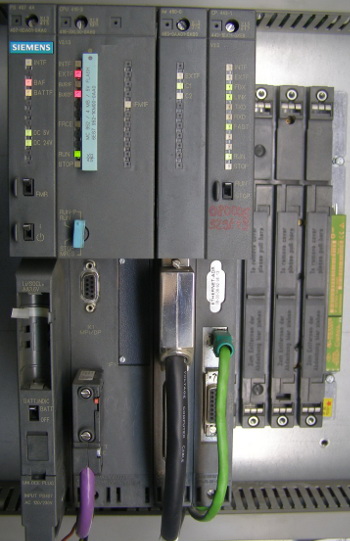 Siemen’s SIMATIC S7-400 industrial automation system. Source: Wikipedia
Siemen’s SIMATIC S7-400 industrial automation system. Source: Wikipedia
Initially designed to be isolated, industrial control systems are now part of an increasingly interconnected network ecosystem. If not directly connected to the internet, industrial systems are often linked with wider plant and corporate networks, exposing them to the risk of cyberattack. Even segregated systems are at risk, as malware can be introduced locally on USB flash drives.
Industrial control systems are often designed with specialized components with decade, or longer, upgrade cycles in mind, making it costly and difficult to adapt to the latest security challenges. A new trend is the industrial internet of things (IIoT) in which sensors connected to a network provide feedback on industrial processes. The IIoT provides a wealth of data that allows plant managers to discover ways to optimize plant processes but also introduces vulnerabilities that can be exploited by attackers to gain access to the industrial control system.
Consequences
Security breaches can have serious consequences, including physical damage and financial loss. In 2014, attackers gained access to the corporate network of a German steel mill through a phishing attempt. The attackers were then able to transition into the industrial control system and compromise control components, which led to the inability of a furnace to shut down safely, causing massive damage.
Financial loss due to software piracy can also result from cybersecurity breaches. Losses in the manufacturing sector due to data breaches resulting in stolen intellectual property totaled $240 billion in revenue, $70 billion in GDP, and 42,220 U.S. manufacturing jobs between 2002 and 2012 according to a 2014 study by Bill Kerr, chief economist for the National Association of Manufacturers.
Threat Vectors
Software piracy is just one threat vector facing industrial companies. Attackers can take advantage of software vulnerabilities to install malware such as viruses, worms, trojans or ransomware. Similarly, unsecured networks can open the door to intrusions and data loss. Wireless connections to industrial networks, such as those used by sensors in IIoT and cloud-based SCADA solutions, can introduce vulnerabilities that need to be secured.
Attackers can also make targeted attacks, such as advanced persistent threats (APTs) and social engineering or spear phishing attempts, in which they seek to manipulate or trick employees into opening risky links or giving away private data like network credentials. Internal security threats are a major problem. Employees can unknowingly grant attackers access to systems by responding to phishing attempts, accidentally introduce malware by opening an infected email attachment, or compromise a critical system by inserting an infected USB stick into an industrial control computer.
Information can also be leaked as a result of stolen mobile devices. In addition, external third parties with access to the network, such as partners or service providers, can introduce additional exposure risk if they do not comply with the security processes of the company.
Security Measures
 Control panel for thermal oxidizer regulation with an Allen-Bradley PLC user interface. Compromising this PLC could lead to catastrophic failure of the combustion process. Source: Wikipedia / CC BY-SA 4.0
Control panel for thermal oxidizer regulation with an Allen-Bradley PLC user interface. Compromising this PLC could lead to catastrophic failure of the combustion process. Source: Wikipedia / CC BY-SA 4.0
The cybersecurity threat that industrial operations face is substantial, but the implementation of various security measures can help to minimize the risk. Anti-malware software should be installed on control system computers, and device access controls should be in place throughout the plant. Control systems and the rest of the network should be separated with the use of air gaps, demilitarized zones, firewalls or unidirectional gateways.
Network monitoring should be performed to capture and analyze all data traversing the network, with specific attention paid to traffic entering and exiting the industrial control system from less secure network areas. With constant monitoring, analysts can detect intrusions and anomalies and take the necessary actions to stop the breach. Audits of industrial control systems security and vulnerability scans should be performed regularly, and the latest security patches should be deployed to computers and equipment on a frequent schedule. In addition, companies need security professionals with the necessary knowledge to implement these protective measures.
Security training is essential for employees to raise awareness of cybersecurity risks and adhere to proper procedures and guidelines when carrying out computer tasks like connecting to the network remotely, downloading files from the internet, or opening email attachments.
Implementing sufficient measures to prevent breaches of security can be challenging. Industrial control systems can have complex architectures that are interconnected with the wider enterprise network. In addition, security awareness among equipment operators can be lacking, there can be a lack of availability of appropriate security products, senior management could consider cybersecurity to be a low business priority or a company could simply lack the budget to properly address the risk.
Another challenge is the lack of government regulations and industry guidelines, leaving companies without clear guidance on how to implement security protections. An absence of reporting requirements can hide the true scale of data breaches as companies attempt to guard brand reputation.
Resources
Kasperky Lab’s State of Industrial Cybersecurity 2017 Report [PDF]




