The smart grid and cybersecurity issues
N. Mughees | January 17, 2022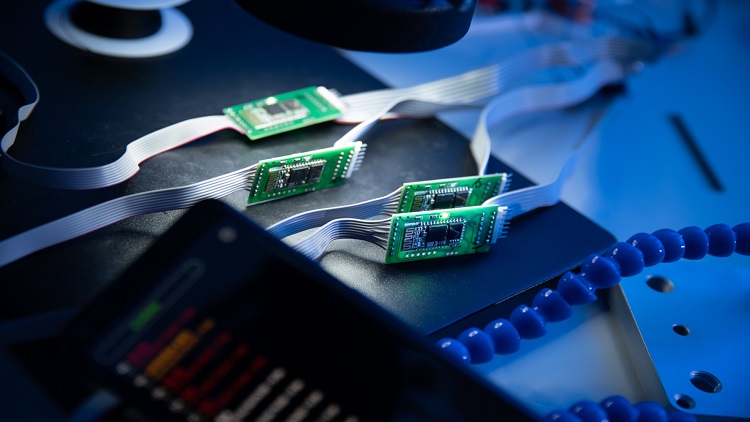 New cybersecurity concerns, particularly in the areas of smart grid privacy and connection, are emerging. Intelligent solutions are on the way. Source: visegradinsight.eu/, Creative Commons License
New cybersecurity concerns, particularly in the areas of smart grid privacy and connection, are emerging. Intelligent solutions are on the way. Source: visegradinsight.eu/, Creative Commons License
Introduction to smart grids
Smart grids are the result of the modernization of the traditional power system infrastructure through integration of renewable energy sources while also using innovative communication and computing technologies. This enables two-way communication between the consumer and the energy provider or source, resulting in improved energy management and distribution as well as increased transparency, efficiency, control and safety to lower costs and increase the reliability, transparency and efficiency of the grid infrastructure. The benefits of two-way communication with the electrical power system cannot be exaggerated: by using communication technologies, it is possible to integrate additional renewable energy sources into the grid to supplement, and in some cases completely replace, traditional non-renewable energy sources.
Cybersecurity issues
Security is critical to the success and widespread adoption of smart grid networks. Because of the network design characteristics and the important nature of applications in terms of delay, personal and sensitive data transfer, smart grids bring additional security concerns. The purpose of this article is to provide an overview of types of cybersecurity issues in smart grids complex architectures and the efforts and standards that address them.
Goals and standards
Smart grid high-level security needs are identical to those of any other system that makes use of a communication network. Confidentiality protects private information from unauthorized access; integrity maintains the accuracy of information; whereas availability ensures service. However, in contrast to standard communication networks, the needs are prioritized in reverse order: availability, integrity and confidentiality. The cybersecurity criteria are meant to ensure that the grid is secure, robust and resilient to threats. Therefore, the grid should include the following strategies: be capable of detecting and responding to threats, include access-control systems to prevent unauthorized access, and define standards for secure communication.
Categories of threats
While communication network integration provides tremendous benefits, it also introduces risks and obstacles in terms of protecting and managing smart grids. Potential and known attacks can be broadly classified into targeted threats, system failure, physical attacks and hybrid threats. There are numerous possible motivations for targeted attacks on the power grid, including hacktivism, cybercrime and cyberwarfare and cyberespionage.
Targeted threats
The malicious computer worm Stuxnet is the most well-known case of a cyber weapon. Its attack vectors target various areas of the smart grid including hardware and software. Stuxnet was created to attack certain Supervisory Control and Data Acquisition (SCADA) systems, resulting in the loss of more than a thousand Iranian nuclear centrifuges, among other things. The malware's subtlety and success have prompted numerous concerns about the safety of such systems. Havex is yet another well-known malware that targets industrial control systems, while the trojan BlackEnergy was identified in computer networks following the Ukrainian blackout and is believed to have played a significant part in the incident. Not all SCADA systems that are connected to the smart grid will be separated and mostly offline. As a result, there is a greater emphasis on the targeted threat itself, as well as on developing measures to defend against similar attacks.
[Discover more about security software on GlobalSpec]
Failure of a system
Besides human error, many power grid failures can be linked to equipment failures, for example, as occurred in the London/West Midlands, North American, South Australian, and Swiss/Italian blackouts. The North American blackout sparked research into techniques for detecting occurrences that could eventually result in cascade failures. Consideration has been given to factors such as power surges and power oscillations, with potential measures to be employed in the event of an impending natural disaster being proposed.
Physical attacks
These attacks may be launched against both live power lines and transformers and substations, but that is unlikely given the dangers. Physical attacks against the smart grid's soft entry points, on the other hand, are more probable. These include smart meters, which are regarded as soft targets because of their widespread availability and use. Until tamper-evident or tamper-resistant design becomes the standard, it is critical to prioritize data and information security on systems. Physical attacks on SCADA systems are more difficult, though by no means unattainable. Such systems are in charge of collecting data such as power flows and transmitting it to the state estimator for the purpose of estimating power and network conditions.
Hybrid threats
Since there are attacks that focus exclusively on the cyber domain or the physical domain, there are also attacks that span both worlds. Such hybrid threats create significant issues not only in terms of defending against them, but also in terms of protocol definition. Protections against these attacks are naturally complex, as an attacker might target any combination of the smart grid's various components.
[Learn more about cybersecurity products and providers]
Conclusion
Building safe solutions for the smart grid will be a continuing process that will evolve in lockstep with technological advancements, since the necessary steps have been undertaken to develop security criteria from the start. A comprehensive information sharing system would be an essential and inevitable step forward in terms of cybersecurity for the smart grid, and so provides an exciting view into the future of intelligent protection for these systems.




