New Analysis Method Finds Internet Browser Security Flaws
Engineering360 News Desk | August 13, 2015Researchers from the Georgia Institute of Technology College of Computing have developed a cybersecurity analysis method that discovered 11 previously unknown Internet browser security flaws. Their findings were honored with the Internet Defense Prize—an award presented by Facebook in partnership with USENIX at the 24th USENIX Security Symposium.
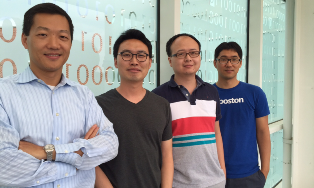 Georgia Tech's winning team at the 24th USENIX Security Symposium are: (from left to right): Wenke Lee, Byoungyoung Lee, Chengyu Song, and Taesoo Kim. Credit: Georgia TechPh.D. students Byoungyoung Lee and Chengyu Song, with Professors Taesoo Kim and Wenke Lee, of Georgia Tech say they will continue their research to make the Internet safer.
Georgia Tech's winning team at the 24th USENIX Security Symposium are: (from left to right): Wenke Lee, Byoungyoung Lee, Chengyu Song, and Taesoo Kim. Credit: Georgia TechPh.D. students Byoungyoung Lee and Chengyu Song, with Professors Taesoo Kim and Wenke Lee, of Georgia Tech say they will continue their research to make the Internet safer.
Their research, "Type Casting Verification: Stopping an Emerging Attack Vector," explores vulnerabilities in C++ programs (such as Chrome and Firefox) that result from "bad casting" or "type confusion." Bad casting enables an attacker to corrupt the memory in a browser so that it follows a malicious logic instead of proper instructions. The researchers developed a proprietary detection tool called CAVER to catch them. CAVER is a run-time detection tool with 7.6%-64.6% overhead on browser performance (Chrome and Firefox, respectively). The 11 vulnerabilities identified by Georgia Tech have been confirmed and fixed by vendors.
"It is time for the Internet community to start addressing the more difficult, deeper security problems," says Professor Lee. "The security research community has been working on various ways to detect and fix memory safety bugs for decades, and have made progress on 'stack overflow' and 'heap overflow' bugs, but these have now become relatively easy problems. Our work studied the much harder and deeper bugs—in particular 'use-after-free' and 'bad casting'—and our tools discovered serious security bugs in widely used software, such as Firefox and libstdc++."
Related link:




