Biometric Security: Your Body as Your Password
Robert Springer | January 04, 2017Login IDs and passwords have been used to access computer and mobile device systems for 65 years, and security professionals say the venerable approach is showing its age.
Late in 2016, for example, Yahoo announced what may rank as one of the largest data breaches in history, with the details of at least 500 million accounts reported stolen.
Security researchers and technology companies are working on methods to better protect users’ information. Biometric security has proven to be an effective and convenient way to bolster security, especially on mobile devices, which have the technology (cameras and fingerprint readers) built-in.
Biometric security has been around for years, but didn’t really take off until Apple introduced a relatively easy-to-use fingerprint reader on the iPhone 5S in 2013. By 2016, mobile customers of financial services firm USAA were able to choose among three biometric authentication methods: facial recognition, fingerprint, and voice recognition.
 Conor White, Daon With more than 2 million users, the company’s biometric security program has proved quite popular, says Conor White, president of the Americas for Daon, a maker of identity assurance software that counts USAA as a customer.
Conor White, Daon With more than 2 million users, the company’s biometric security program has proved quite popular, says Conor White, president of the Americas for Daon, a maker of identity assurance software that counts USAA as a customer.
Experts say that mass adoption of biometric security could prevent breaches such as the one at Yahoo. That’s because biometric data is not stored on a centralized, potentially hackable server in a data center. It’s also more convenient, as a fingerprint swipe is quicker than entering a password containing numbers and characters on a small screen.
While biometric security is harder to hack and potentially more convenient than password protection, the technology must still overcome user inertia as well as some growing pains to challenge passwords and gain widespread usage on mobile devices.
Private Cryptographic Keys
Mobile biometrics are fundamentally different from traditional security in that “it’s all about liveness detection.” In other words, the objective is to make sure that the person holding the phone is a real person and not a fake or an imposter. “You cannot do that with a password,” says White.
What’s more, biometric data is not stored in any identifiable way on the mobile device. Instead, it’s stored in a protected area of the device. The only data that is sent over the cellular or Wi-Fi network is a private cryptographic key that certifies the user’s identity.
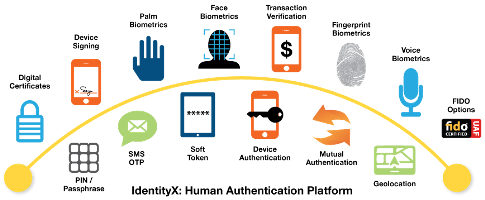 (Click to enlarge.) Elements of an authentication platform. Image source: DaonOnce a user has set up biometric security on his or her device (via Apple’s Touch ID for fingerprints, for example), an app like PayPal can leverage it for authentication.
(Click to enlarge.) Elements of an authentication platform. Image source: DaonOnce a user has set up biometric security on his or her device (via Apple’s Touch ID for fingerprints, for example), an app like PayPal can leverage it for authentication.
“When you swipe your finger, the system has verified that it is PayPal who’s asking,” says Rajiv Dholakia, vice president products and business development at Nok Nok Labs, a biometric authentication software company.
 Rajiv Dholakia, Nok Nok LabsDholakia says that it will look for the PayPal private key, then find the challenge that has been sent from the PayPal server, and then respond to that challenge with the private key. It can then be verified by PayPal on the server that this is indeed the expected user and device. “All of the biometrics remain on the client side; nothing has come up stream,” Dholakia says. (PayPal is a Nok Nok customer.)
Rajiv Dholakia, Nok Nok LabsDholakia says that it will look for the PayPal private key, then find the challenge that has been sent from the PayPal server, and then respond to that challenge with the private key. It can then be verified by PayPal on the server that this is indeed the expected user and device. “All of the biometrics remain on the client side; nothing has come up stream,” Dholakia says. (PayPal is a Nok Nok customer.)
Mobile Biometric Data Security
Due to the way they’re stored and protected (sometimes in clear text), user IDs and passwords can be compromised, sometimes in alarming numbers. Biometric data is not stored in an identifiable way on a mobile device, so even if a hacker obtains the device the information is almost impossible to retrieve.
The fingerprint-matching system on an iPhone is a “standalone thing,” says Dr. Mikhail Gofman, an associate professor and director of the College of Engineering and Computer Science Center for Cybersecurity at California State University-Fullerton. The iPhone’s Secure Enclave processor protects fingerprint data at the hardware level. “It cannot really exchange any data with the main system so they have a very strict communication channel,” he says. iOS, the iPhone’s operating system, is effectively cut off from biometric data, making hacking it difficult.
 Mikhail Gofman, Cal State FullertonAdditionally, fingerprints are hard to duplicate and then use, says White. Not only does a thief need the user’s device, but he or she also needs a valid fingerprint and a way to recreate it (a gelatin mold or rubber finger) to access the device.
Mikhail Gofman, Cal State FullertonAdditionally, fingerprints are hard to duplicate and then use, says White. Not only does a thief need the user’s device, but he or she also needs a valid fingerprint and a way to recreate it (a gelatin mold or rubber finger) to access the device.
Multimodal Biometric Security
Multimodal biometric security allows authenticators to ask for multiple biometric authentications before access is granted. A user may be asked to read a sentence while looking into the device’s camera, for example, allowing authentication via face and voice. Multimodal biometrics are difficult to spoof as simply holding up the user’s picture for facial authentication will fail as a voice (and moving lips) or fingerprints also are required, says White.
The promise of multimodal biometrics can also be its Achilles’ heel, as “certain biometrics lend themselves to certain use cases more so than others,” White says. For example, if the user is at a party, facial and voice recognition might not work if the lighting isn’t adequate and ambient noise is too loud. The user would need to find better lighting or find a quieter room to get multimodal biometrics to work.
“So, now we're asking the user to capture multiple biometric modalities to access their device, and that's less convenient, and of course whenever convenience suffers, the users are turned off,” says Gofman. “We’re looking for user-friendly ways of implementing multimodal biometrics.” The bottom line, he says, is to make it easy, make it secure, and make it cheap.
Barriers to Adoption
Despite the relative convenience and improved security that biometric security offers mobile users, usability and data protection concerns are slowing the technology’s adoption, says Dr. Damon Woodard, an associate professor in the Electrical and Computer Engineering Department at the University of Florida.
 Damon Woodard, University of Florida“Usability is of major concern to mobile device users, and in some situations is more important than security,” he says. Users are more familiar with passwords and PINs. They also tend to discount the threat to the security of their devices, which mainly comes from theft (an affects 2 to 3 million devices per year).
Damon Woodard, University of Florida“Usability is of major concern to mobile device users, and in some situations is more important than security,” he says. Users are more familiar with passwords and PINs. They also tend to discount the threat to the security of their devices, which mainly comes from theft (an affects 2 to 3 million devices per year).
Some users are also concerned that “once biometric data is compromised, it cannot be reset, unlike a password or PIN,” says Woodard. “The risk of this scenario can outweigh that of a security breach involving data stored on a mobile device, thus affecting their choice to use biometrics to secure the mobile device.”
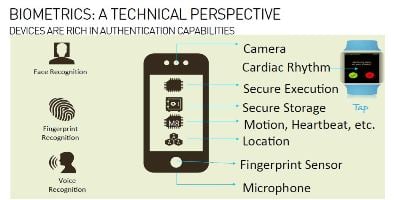 (Click to enlarge.) Building blocks for authentication. Image source: Nok Nok LabsExperts predict, however, that the use of mobile biometric security will continue to grow as phone manufacturers and app producers make the technology more attractive to users than traditional passwords.
(Click to enlarge.) Building blocks for authentication. Image source: Nok Nok LabsExperts predict, however, that the use of mobile biometric security will continue to grow as phone manufacturers and app producers make the technology more attractive to users than traditional passwords.
Gofman says that software can only do so much to make multimodal biometric security more user friendly, so it’s incumbent upon hardware manufacturers to do their share.
“If engineers start looking into a way to design a device that specifically designed around the idea of being multimodal-biometric friendly – where do you place the sensors, what type of cameras you support – it would make it much easier for software people to implement user-friendly solutions,” he says.
Improved sensor technology will increase usability by reducing failure to acquire (when the biometric sensor can’t “read” the user’s input) and failure to enroll (the user can’t establish a biometric security marker) rates, according to Woodard.
White says that devices like desktop and notebook computers are playing catch-up to their smaller brethren, as a financial services password entered on a notebook over an unsecured Wi-Fi connection is more vulnerable to hacking than a cryptographic key sent from a mobile device.
After decades of causing grief for users, perhaps a password-less future is not that far off.





This is really positive and has applications for proving our personal identity in many situations. Most importantly, this might save us from having to have RFID tags implanted.
Fingerprints are widely spread as biometric security password. It is interesting when we would use an express DNA analysis.